Define the boundary first
Start with who needs access, what device or service is targeted, and whether traffic crosses public networks.
Casebook
Covering home remote desktop, solo developer cloud access, home surveillance, multi-region server mesh, factory equipment networking, and collaborative operations with a consistent presentation structure.

Methodology
Start with who needs access, what device or service is targeted, and whether traffic crosses public networks.
Encode ACLs, identity verification, and time windows in each case so connectivity stays controllable.
Use connection success rate, latency stability, and audit traceability to measure outcomes and support continuous optimization.
Scenarios
Each case includes challenge, architecture, security controls, expected outcomes, and topology visualization.
Home remote work
When away from home, connect securely from a laptop to your home workstation for coding, design, and file work.
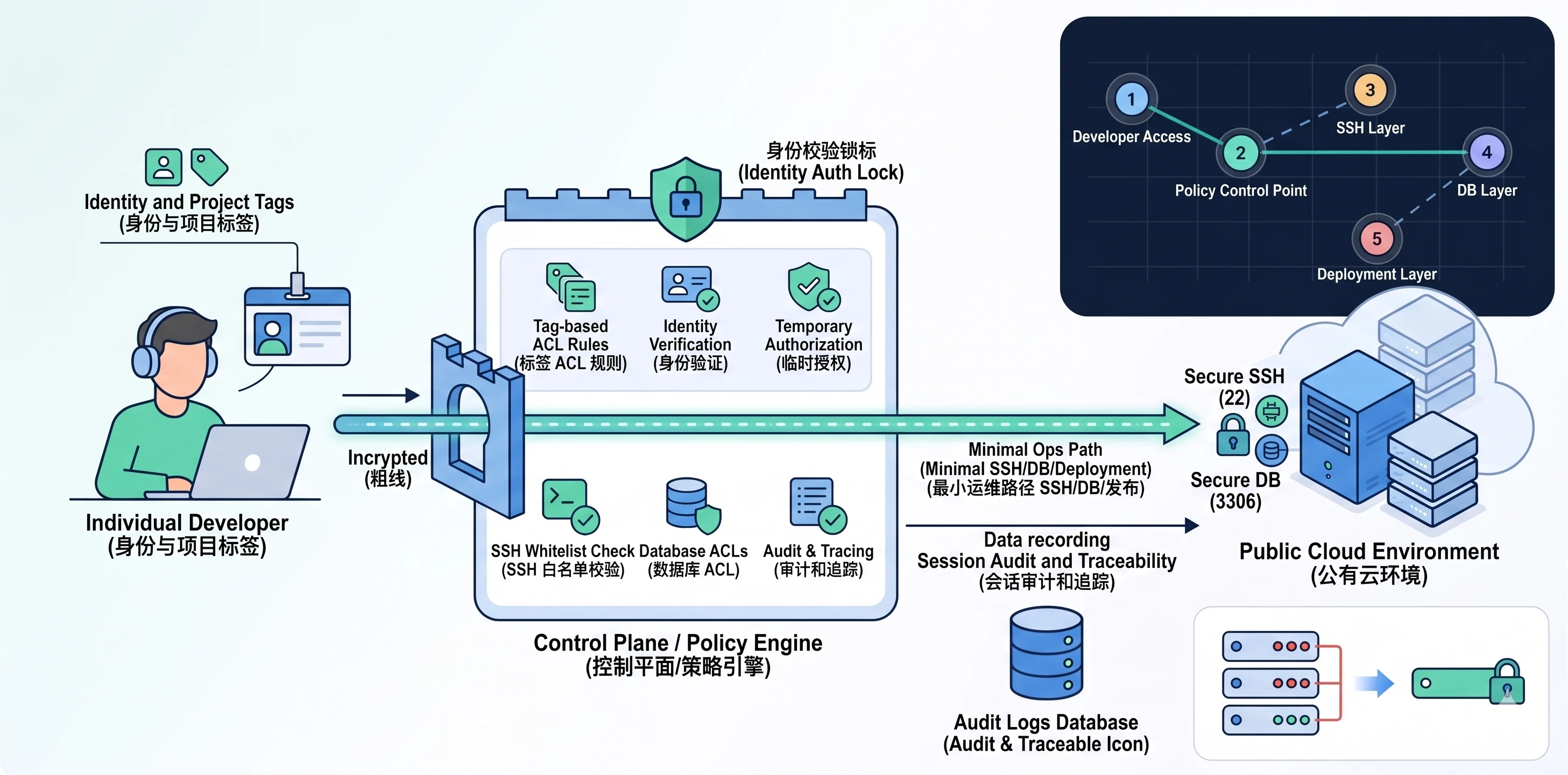
Solo developer
For personal projects on public-cloud VMs, SSH, DB maintenance, and releases must stay secure, auditable, and private.
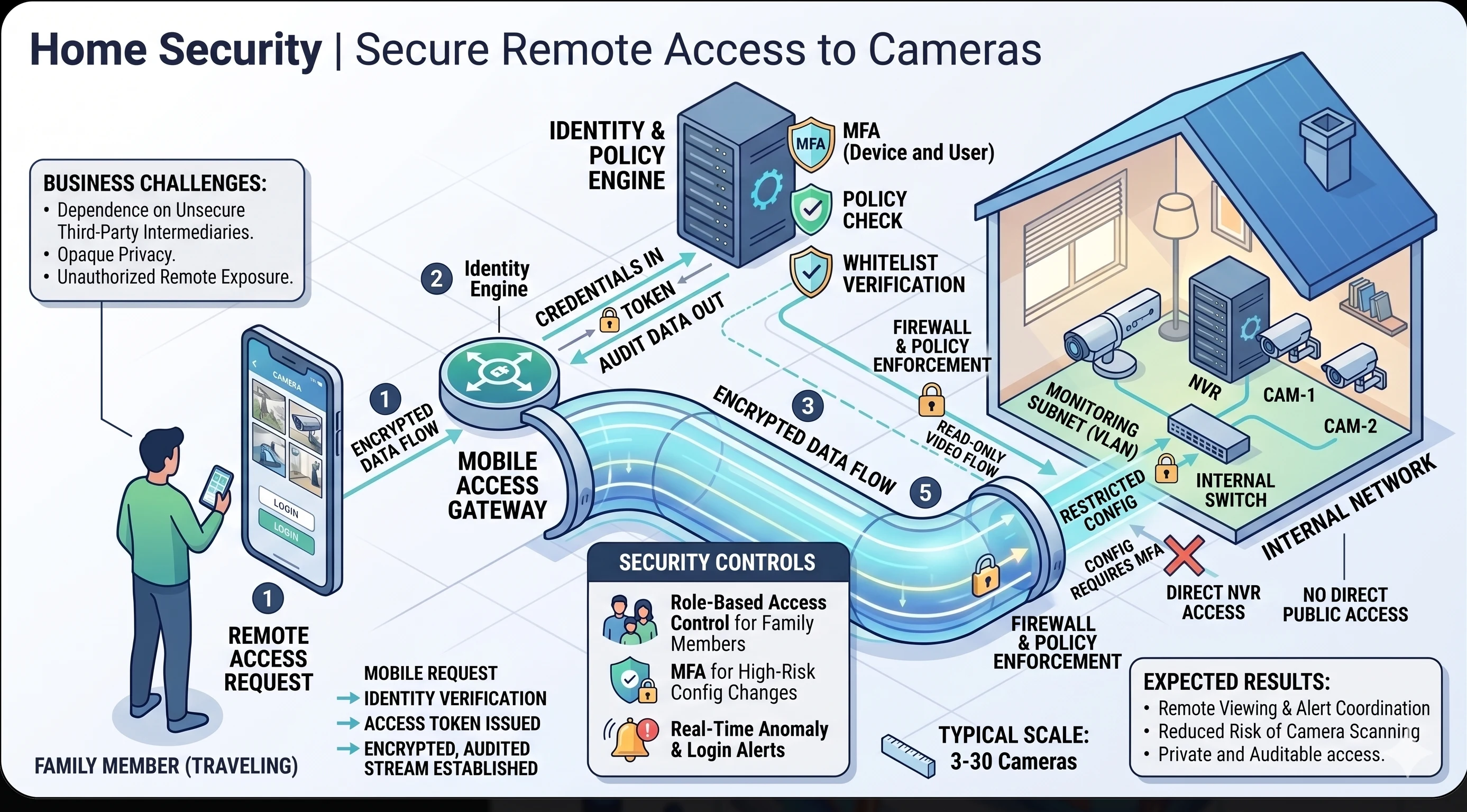
Home surveillance
View NVR and camera feeds from mobile devices without exposing surveillance admin ports to the public internet.
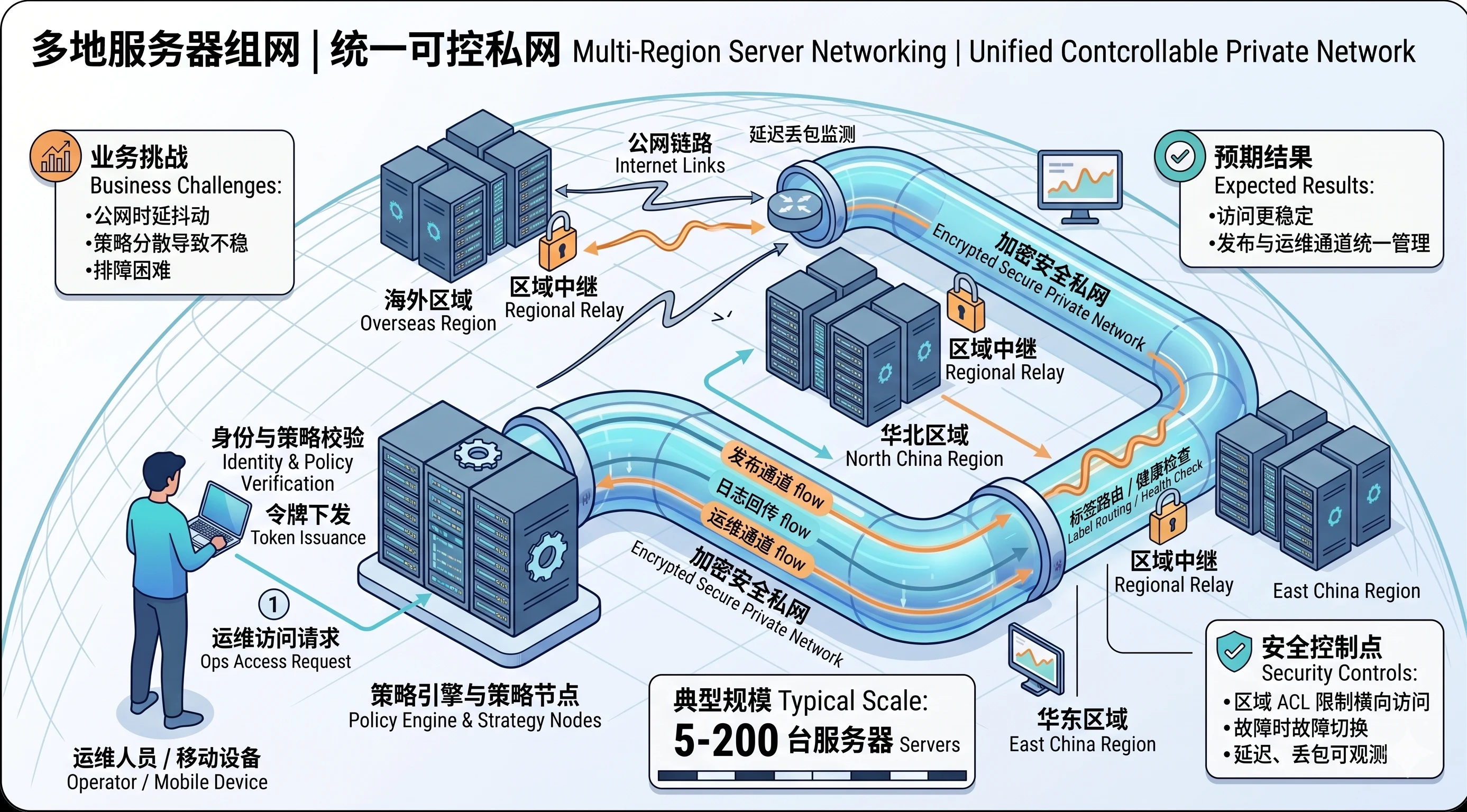
Multi-region server mesh
Bring East China, North China, and overseas servers into one controllable private mesh for release, logging, and cross-region ops.
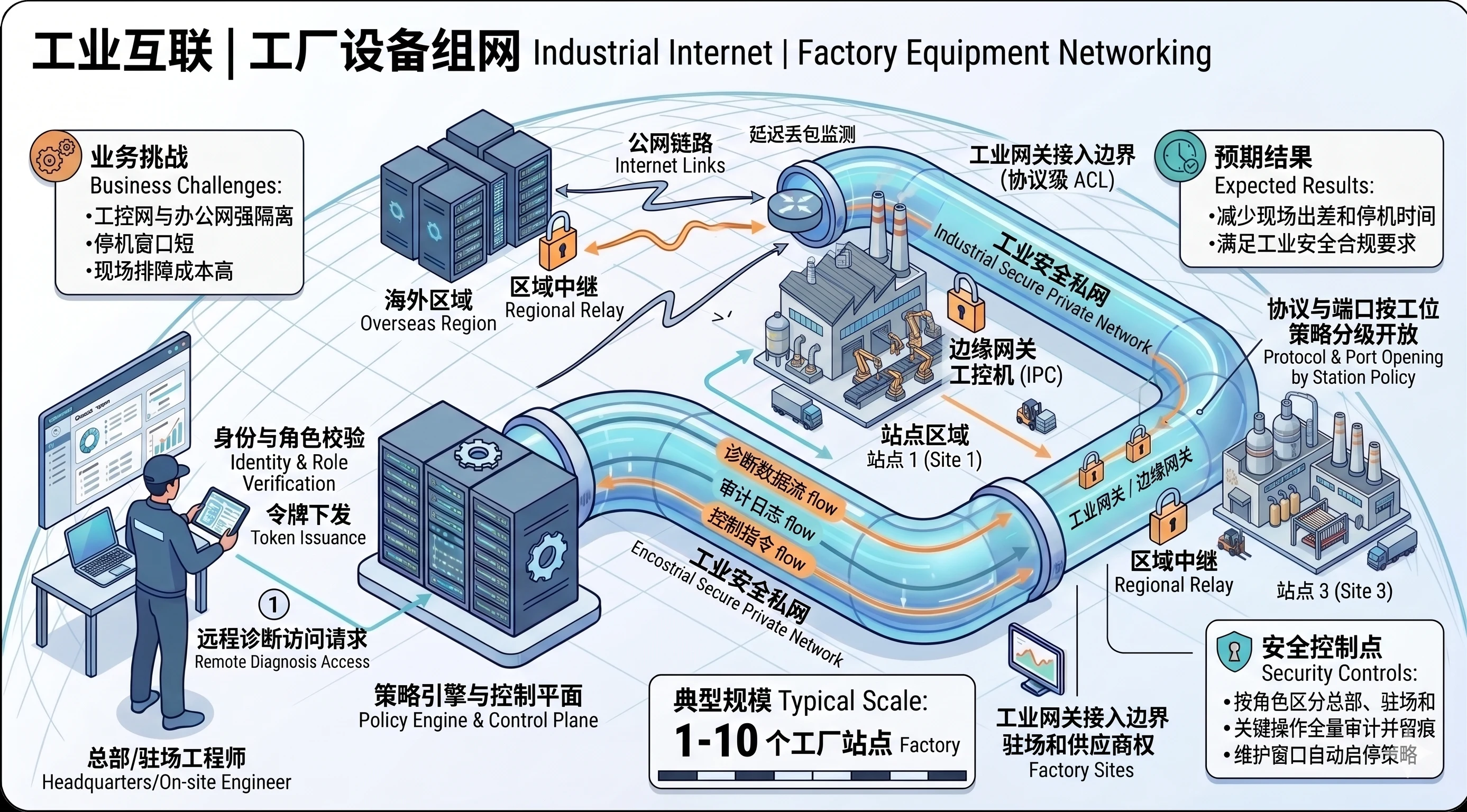
Industrial networking
Onboard PLCs, edge gateways, and industrial PCs into a secure mesh so HQ and field engineers can diagnose remotely.
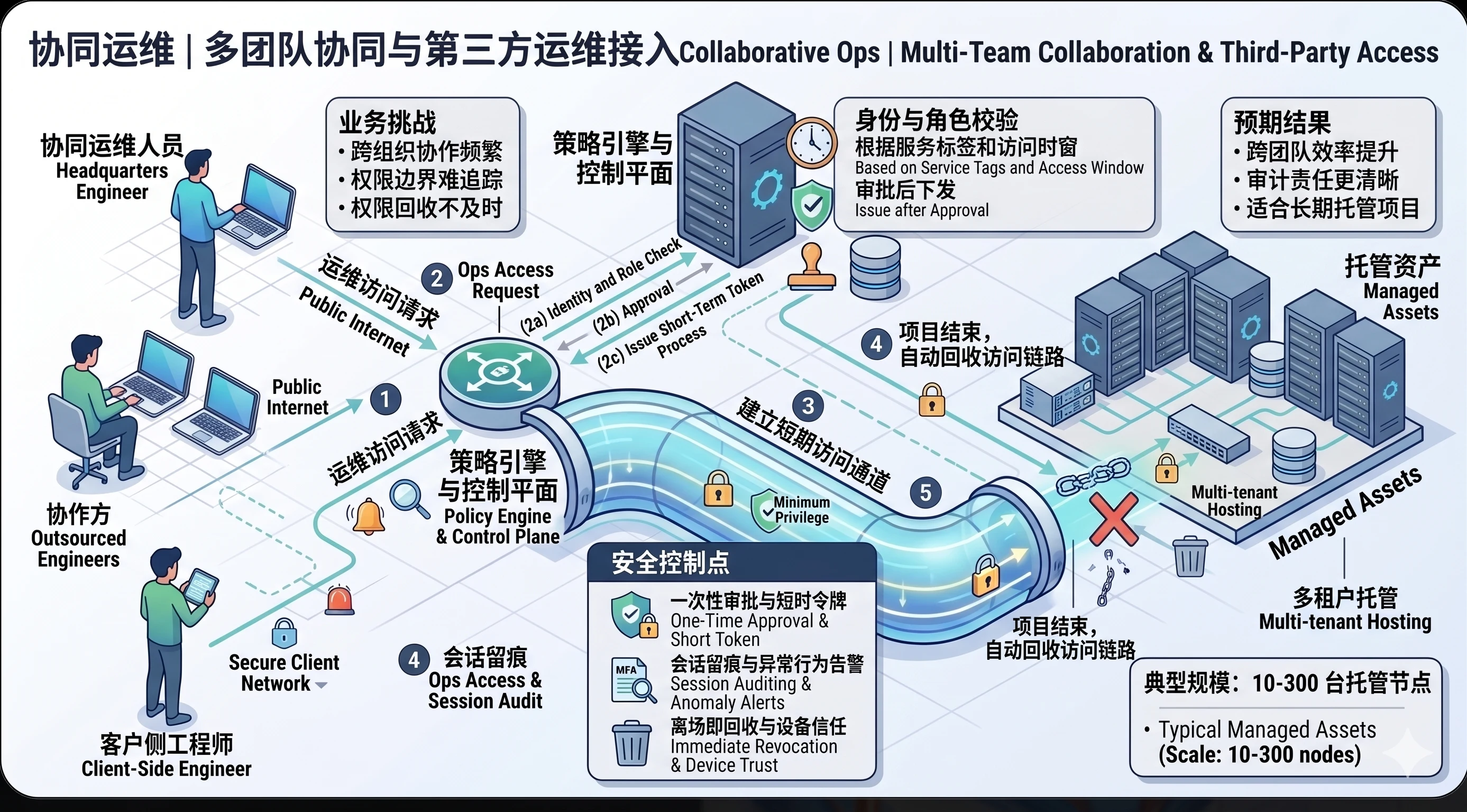
Collaborative operations
HQ teams, contractors, and customer engineers collaborate on the same environment without shared accounts or over-permissioning.
Built on a consistent structure, this page supports solution communication, implementation planning, and operations optimization.